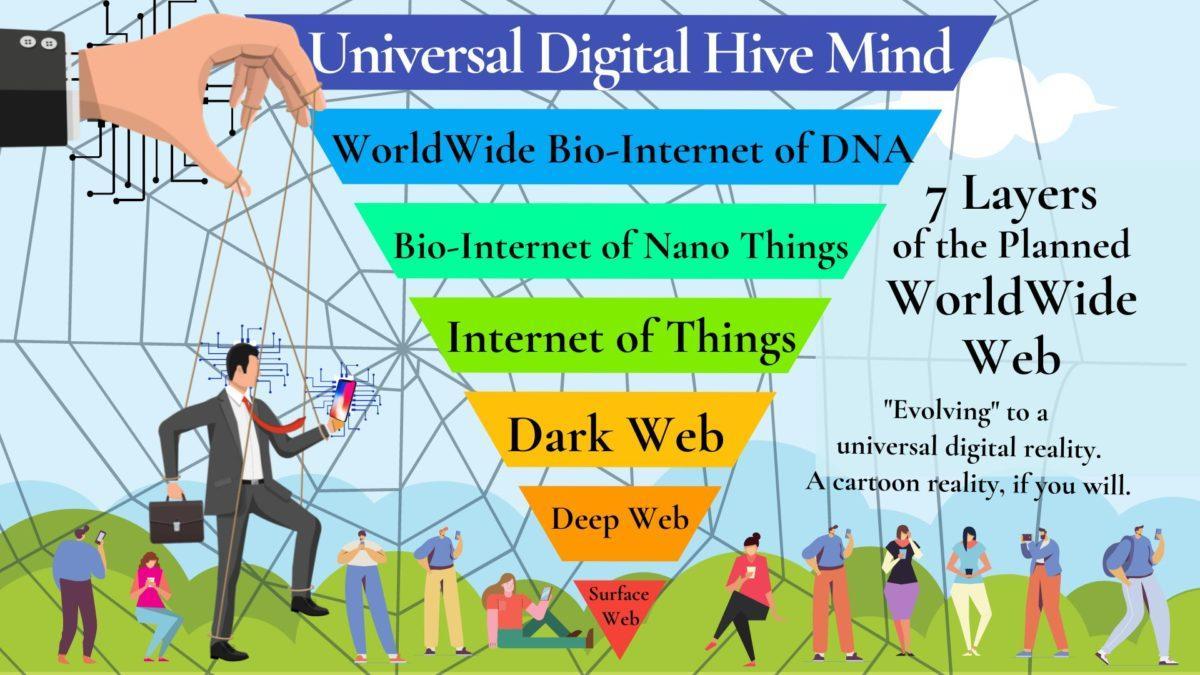
Do any of us really GET the power of the Worldwide Web? Our search engines touch only a fraction of its vast labyrinths, which include the Surface Web, Deep Web, Dark Web, Internet of Things, Bio-Internet of Nano things, the World Bio-Internet of DNA Data, and the Universal Digital Hive Mind. Please know the internet and cell phones are playing a CENTRAL role in the battle for the human mind. Sorry, I’m getting ahead of myself.
When I started to research this topic with my usual innate curiosity, I had no concept of the revelations I would uncover. My surprising discoveries below confirm my conviction that we are living in times of vast change and great risk. As we surf the web every day, we are like innocent children unknowingly playing with the most dangerous toys. Stay with me here – it’s important. I suggest you start with the summary below, and take one section at a time. This could be part of your wake-up call, like I was for me. The tools are useful, and our life-or-death choice is very real. Fasten seatbelts.
Sometimes we hear the words of John Perry Barlow (1947-2018), who devoted his life to making the Internet into “a world that all may enter without privilege or prejudice accorded by race, economic power, military force, or station of birth . . . a world where anyone, anywhere may express his or her beliefs, no matter how singular, without fear of being coerced into silence or conformity.”
Barlow knew that new technology could create and empower evil as much as it could create and empower good. He made a conscious decision to focus on empowering the good “Governments of the Industrial World, you weary giants of flesh and steel, I come from Cyberspace, the new home of Mind. On behalf of the future, I ask you of the past to leave us alone. You are not welcome among us. You have no sovereignty where we gather.” – John Perry Barlow, from “A Declaration of the Independence of Cyberspace”.
Summary:
- What are the Seven Layers of the Internet? Surface Web, Deep Web, Dark Web, Internet of Things, Bio-Internet of Nano Things, World-Wide Bio-Internet of DNA Data, and the Universal Digital Hive Mind. Yikes!
- What’s the Best Search Engine for Your Query? Aha! The all-important question on the Surface Web. Here are my favorite uncensored Search Engines for Independent Thinkers.
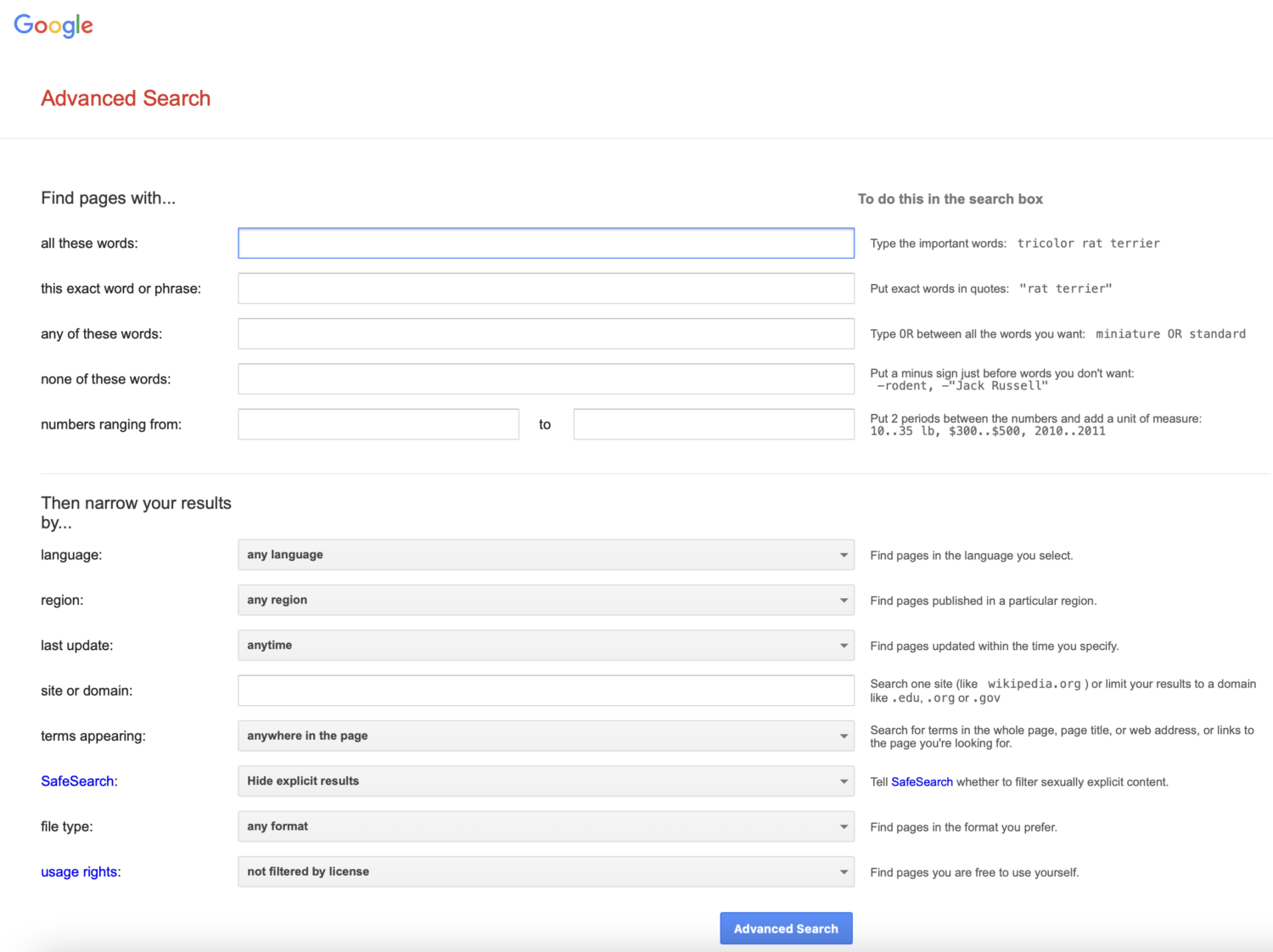
- What’s Your Search Plan? Narrow your focus with Google Advanced Search.
- “Dorking” Makes You an Instant Expert! Use these 35 Operator CODES to Speed Your Search.
- Other Searches – How to Go Deeper? Learn about the Internet Archive Wayback Machine , Geographical, Genealogy, Searching Social Networks, Indexes, Open Source Intelligence (OSINT), More Tricks and Shortcuts.
- The Deep Web is a Huge Resource of Un-indexed Data.
- The Dark Web uses Anonymous TOR Browser and a VPN. Beware!
- The Internet of Things (IoT) – The Great Reset Connectivity of all digital machines via nodes.
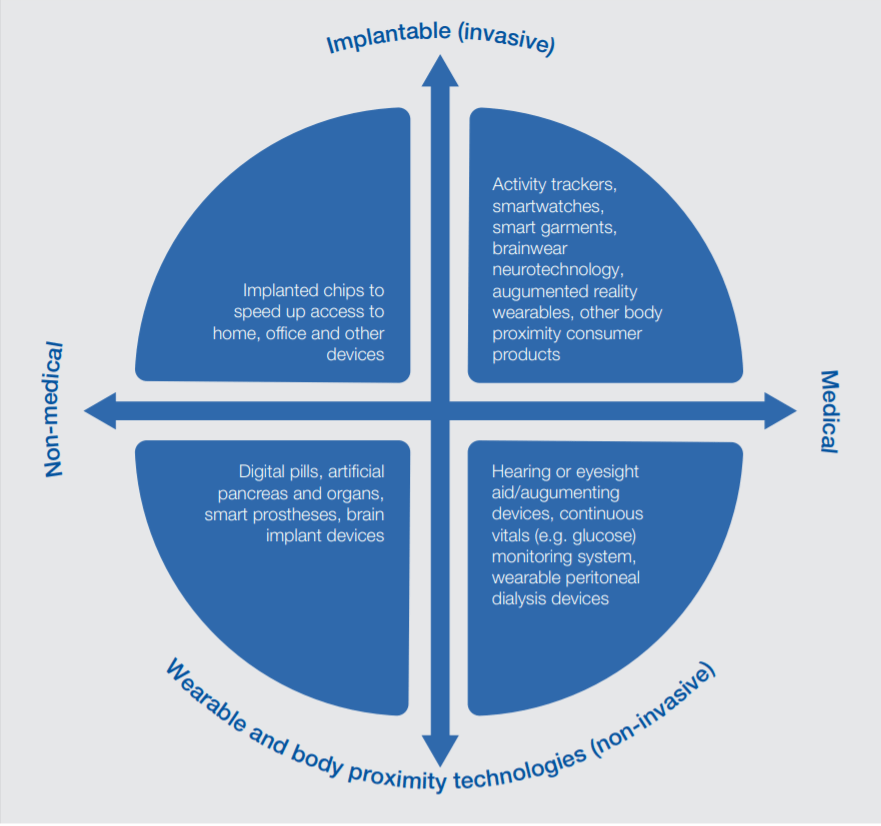
- Bio-Internet of Nano Things and Smartdust- What if the Real Internet is Humans, Bacteria, and all the rest?
- World-Wide Bio-Internet of DNA Data – This is a Planetary Biosphere Network of Observation and Control.
- Bill Gates vs. Steve Jobs on the future of the world. What’s the difference? The Universal Digital Hive Mind of Transhumanism Is Here Now, in Your Body and Soul.
- What was Apple Founder Steve Jobs’ Warning to the World in the film “John Carter”?
- Connecting the Dots: Use Your Biofield as Your Sacred Resource for Universal Source Consciousness of INTENT. The human biofield Just Became a DNA-Generated body part.
1. What are the Seven Layers of the Internet?
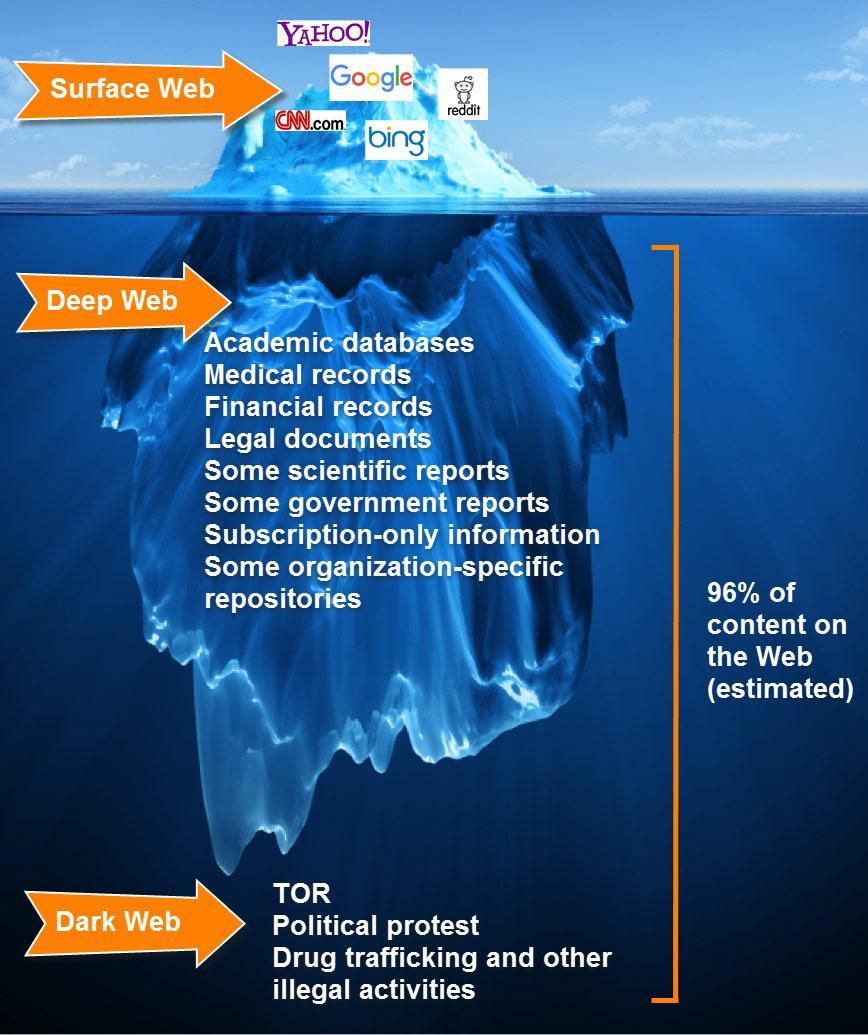
 Surface Web, Deep Web, Dark Web, Internet of Things, Bio-Internet of SmartDust, WorldWide Bio-Internet of DNA Data, Universal Hive Mind. Are you ready?
Surface Web, Deep Web, Dark Web, Internet of Things, Bio-Internet of SmartDust, WorldWide Bio-Internet of DNA Data, Universal Hive Mind. Are you ready?
The Surface Web is what we use every day.
But this represents a tiny fraction all internet content. Fortunately, the Surface Web is indexed by search engines like Google, Bing, Yahoo, etc., so we can find YouTube, Articles, Blogs, Websites, Journals, etc. The Surface Web is all publicly accessible, so it’s more likely to be true.
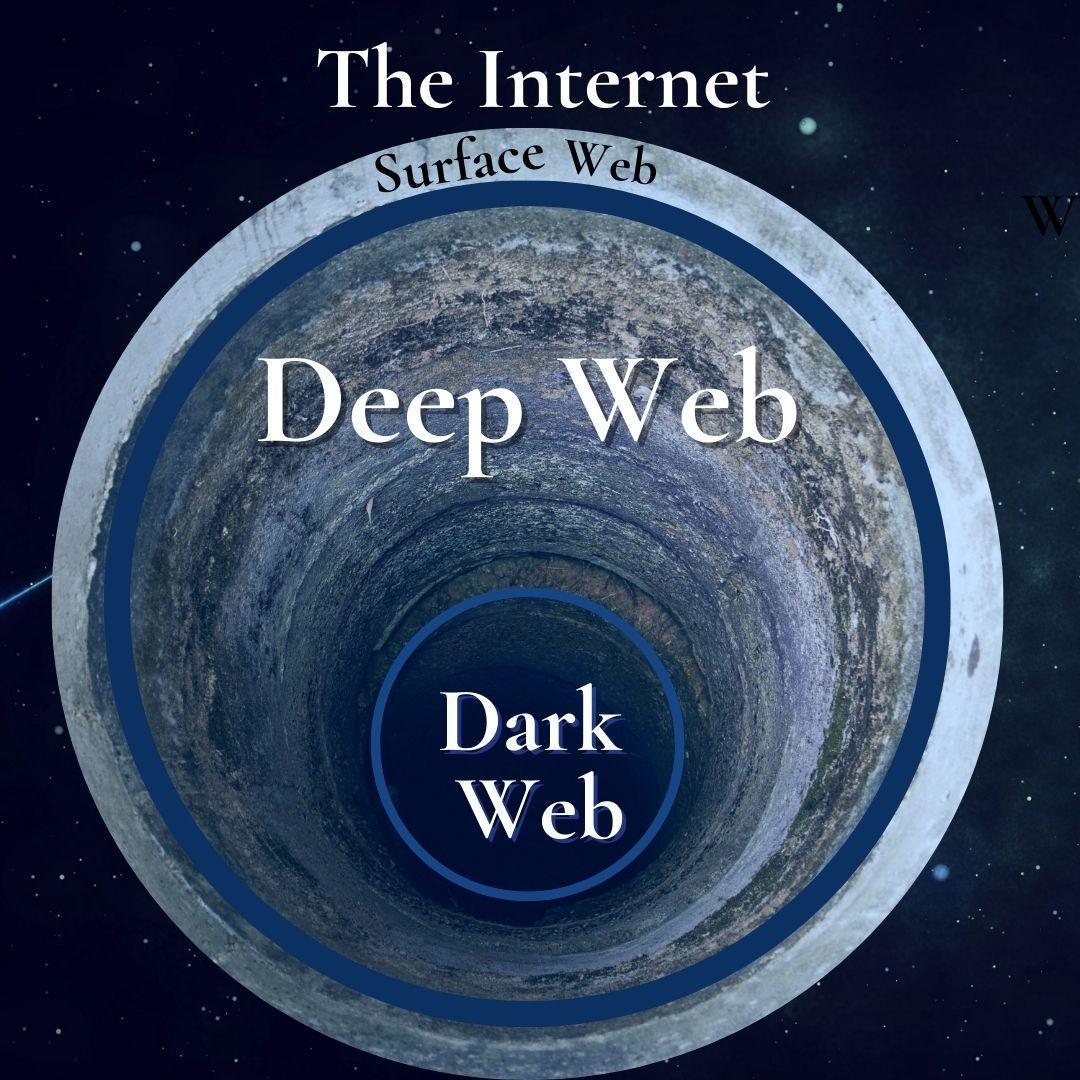
The Deep Web is Unindexed Data
The Deep Web and the Dark Web together make up the 96% of the internet, and they are unavailable to search engines. These two are very distinct. The Deep Web refers to any web page that can’t be directly indexed by a search engine. The Deep Web contains emails, bank statements, and company’s internal databases.
What is the Dark Web?
The infamous Dark Web is anonymous content accessible with specific software. The most popular search engine software to access Dark Web information is TOR, which uses worldwide proxy servers to give the user completely anonymous browsing.
We’ve all heard scary tales of the Dark Web but in reality, it’s just a place where users can remain anonymous, work alone, and find hidden information. Users can search freely without cookies tracking them, and the Dark Web allows for a free exchange of ideas without fear of persecution.
The Internet of Things is the potential interconnectivity of all electrical devices.
Bio-Internet of Smart-Dust is the connectivity of all humans and devices in a unified controllable network, via nano sensors and cellular information.
WorldWide Bio-Internet of DNA Data is the Not-So-Secret Wet Dream of the elite and their Minions, a controlled digital shared 6G “in a “Universal Hive Mind”.
So, What is Your Wish?
Just like the genie in Aladdin’s magical lamp, the web will almost always grant your wish. You’re free to find any data and connect the dots in your own way. That is why careful discernment is critical. The Worldwide Web is for humans exchanging digital information, therefore we can expect much of it to be somewhat twisted, mistaken, and money driven. The only way to surf successfully is to use care, selectivity, and have a good intuitive sense for good information vs. garbage.
2. What’s the Best Search Engine for Your Question?
 If you’re searching the Surface Web, this is the all-important choice.
If you’re searching the Surface Web, this is the all-important choice.
I have my favorites, and I’ll tell you why. Here’s a quick summary of my article: BEST SEARCH ENGINES FOR INDEPENDENT THINKERS. Read it here: https://fiveseasonsmedicine.com/best-search-engines-for-independent-thinkers/
We live in a world on fire with differing opinions. What do you look for in a search engine? If you’re intent on seeing all sides of an issue to make up your own mind, you’d better be VERY selective. Are you guided by your own inner compass and integrity? Or do you prefer a “sanitized” search that follows the government or MSM party line? I’m keenly interested in health. When I’m doing in-depth research, which search engine should I use?
I value my personal thoughts. I believe they are my own. The process by which I form conclusions is unique and complex. I also support YOUR independent thinking, even if it may completely disagree with mine. I need a search engine that shows me ALL sides of a question. I use a variety of search engines. I like to test them to see if they’re showing me the big picture. Some of them limit my searches, some even BLOCK me or PROMPT me as if they would create thoughts FOR me.
Great news! My TOP Favorite is GIBIRU!
GIBIRU search engine shows “Censored Content” side-by-side with “All Content”. This makes Gibiru my favorite search engine for finding ALL INFORMATION on the free web, even the hidden things Google doesn’t want us to see! Try it now! https://gibiru.com/
My Second favorite is Yandex. It is fast, efficient, and appears to be impartial. I like to use a variety of search engines and compare the results.
What are the qualities of a good search engine?
Well, it should be fast, efficient, easy to read. It should be uncensored, not influenced by politics or business. It should not collect my personal data or scan the files on my computer. It should be privately owned, not owned by a Fortune-500 company like Vanguard or BlackRock. It should not sell my search statistics. It should not create personalized ads for me based on my other searches, like I saw recently where Google offered me hotel accommodations in Asia! Ha Ha!
Recently I’ve noticed certain subjects are missing or “hidden” in Google. I notice subjective, opinion-based “science”, in which my searches for medical information are “prompted” or skewed by pharmaceutical interests. Yikes!
Imagine the power a search engine wields, with the ability to influence how people think, our opinions, politics, religion, and even “seed” new thought forms.
How do you control public thought in a war for the human mind? By controlling the information available—and Google has been doing that for a long time. Google, Facebook, Twitter all do this. Compare search engine results, and you’ll see a big difference. Google’s parent company, Alphabet, has become the #1 world leader in molding public opinion on everything from healthcare to politics to AI and human cloning.
 Beware that Google Chrome comes with a “SOFTWARE REPORTER TOOL” which basically SCANS your computer drives and reports back to Google what you have in your computer. Marvelous, isn’t it? A POS browser spying on me! Firefox basically declared they will do the same. Now you understand why I recommend these search engines.
Beware that Google Chrome comes with a “SOFTWARE REPORTER TOOL” which basically SCANS your computer drives and reports back to Google what you have in your computer. Marvelous, isn’t it? A POS browser spying on me! Firefox basically declared they will do the same. Now you understand why I recommend these search engines.
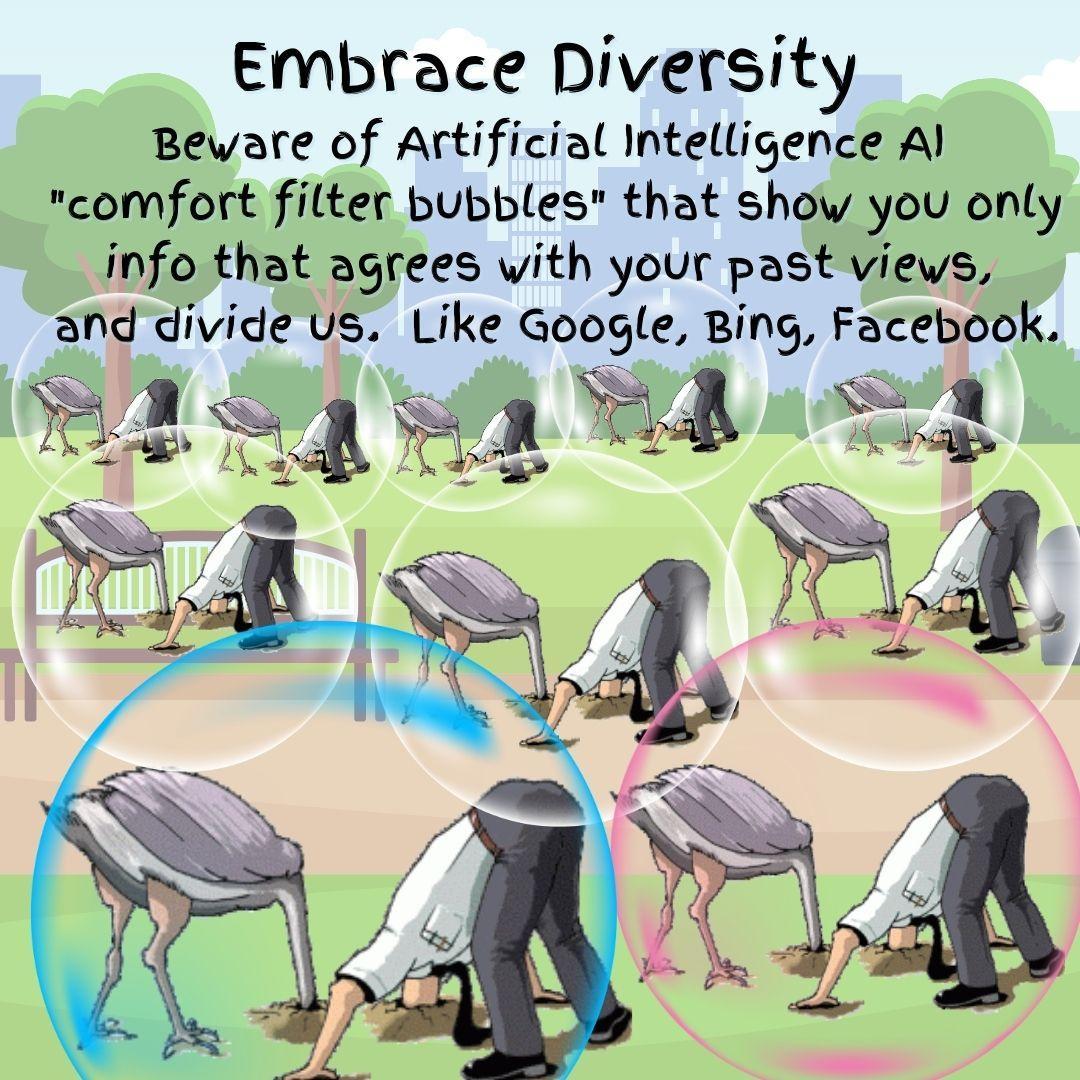
Beware of “Personalized” results and “filter bubbles” from Artificial Intelligence.
Some search engines such as Google and Bing provide customized results based on the user’s activity history, called a “filter bubble”. They use AI algorithms to predict what information you’d like to see, based on your location, past searches, and click history. So, they show only information that agrees with your past viewpoint. Examples are Google’s personalized search results and Facebook’s personalized news stream. This puts the user in a state of intellectual isolation with no contrary information. So, if we get less exposure to conflicting viewpoints, we can exist comfortably with our “heads in the sand”, fully isolated in our own information filter bubble. Some competing search engines seek to avoid this problem by not tracking or “filter bubbling” users.
DuckDuckGo lost my vote when they caved into pressure from authorities to censor articles expressing political opinions. Also, a former employee emailed me that the owner of DuckDuckGo actually DOES sell its search statistics, and I lost confidence in its integrity. To make matters worse, we know DuckDuckGo’s primary algorithm is from Bing by Microsoft, which is already questionable.
There are 100 largely uncensored, unfiltered, unblocked alternatives to Google, Bing, Yahoo. The following Search Engines seem to be, circa 2022, the most uncensored, unblocked of all “uncensored” Search Engines: Yandex.com, Rambler.ru, Startpage.com, Search.meta.ua, Parseek.ir, Mail.ru, Kvasir.no, Boomle.ru, Cluuz.com, Fireball.com, Metabear.ru and DuckDuckgo.com.
Learn More about Alternative Uncensored Search Engines
https://www.olivebiodiesel.com/censortest/#tutorial
Note that what is uncensored and unfiltered in a Russian Search Engine, is often censored in the West, and vice versa. Sometimes, Yandex Advanced, Yahoo Advanced, Google Advanced and WebArchive.org were helpful. So was using the Tor Browser and Torch Uncensored Unfiltered Unblocked Search Engine, etc.
My favorite SEARCH ENGINES for independent thinkers. Click them to TRY:
-
GIBIRU – https://gibiru.com
-
YANDEX – https://yandex.com
-
BRAVE – https://search.brave.com
-
SWISSCOWS – https://swisscows.com
-
PRESEARCH – https://presearch.com
-
ECOSIA – https://www.ecosia.org
3. What’s Your Search Plan?
If you have an important question, and especially if you’re doing research, you need a plan for gathering information. What does that include? Think about what exactly you are looking for and where to find it. Searches should be methodical, efficient, and relevant.
A search plan consists of three steps:
- Analyze your research topic to identify action words for what to do, like “discuss”, “compare”, “describe”.
Look for constraints, to narrow the focus of your search, such as “during the last twenty years” and “in Germany”.
Determine the keywords, concepts, or hashtags that describe your topic. Look for synonyms to expand the search field.
Add a “crazy wild card” to eliminate generic, similar articles, and to allow free-thinking articles. For example “independent” or “unconscious” or “coconut oil”. - Determine what type of information you need. What are your sources, and where you might find that type of information?
- Prepare your search queries for the web. Write out your search plan, try different search engines, and be open to change it as you go.
Narrow Your Focus with Google Advanced Search
4. “Dorking” Makes You an Instant Expert.
Learn these 35 “Search Operator Codes” to Speed Your Search
Everybody needs to know how to use search engines. When you need to find specific information on Google, especially unusual information you can just use Google’s built-in Search Operators. This helps you limit your results to cut through the internet’s vast data to find the information you need. Read the 35 codes below, or here’s a video to help you quickly:
What’s a Search Operator, or a “Dork?
These are symbols or words to make your search results more precise.
They are coded shortcuts to get better results by narrowing down the results in a specific way. So instead of getting pages of unrelated results, you get only results that are relevant to what you want. Here’s a list of All Google Dorks.
https://www.boxpiper.com/posts/google-dork-list
There are so many “Dorks”. Let’s just learn them:
- When you want EVERY result possible, just enter the search words. Ex: USA university
Note: Do NOT enter non-essential words in your search, such as “What is the meaning of the term Dork?” - Narrow your search with more specific words
USA university Geology  Narrow your search using “quotes” to exactly those that contain a specific string of words.
Narrow your search using “quotes” to exactly those that contain a specific string of words.
USA university “Geology 101”- Use a minus sign – to Exclude words
USA university “Geology 101” -Kentucky - Or exclude Many words
USA university “Geology 101” -Kentucky -Tennessee - Exclude exact match phrases
USA university “Geology 101” -Kentucky -Tennessee –“satellite imaging” - Exclude multiple phrases
USA university “Geology 101” -Kentucky -Tennessee –“satellite imaging” -satellite images” - Select for EITHER OR:
USA university “Geology 101” -Kentucky -Tennessee –“satellite imaging” –“satellite images” Iowa OR Minnesota
You can also use the vertical pipe symbol (|) in place of OR. - USE OR for phrases:
“satellite imaging” OR “satellite images” - Get more phrase results with wildcards, using an asterisk (*).
“Wildcard” in a phrase means that position can be anything in the phrase - For example, if you wanted to talk about Happy Christmas Season, but also Happy Holiday Season:
“Happy * Season” - Include words
“Happy * Season” +children - Include phrases
“Happy * Season” +“red poinsettia” - Find words that are AROUND or near each other:
This is the AROUND(X) operator. Find results where your search terms are close to each other.
Use an X for how many words at most can separate the two terms.
So, for example, if you use this query: College AROUND(9) professor
You’ll get results where College and professor are within 10 words of each other.
This is useful if you need results that connect two topics. - Use the AROUND(X) operator with “quotes” to find phrases near each other.
Ex: “University faculty” AROUND(9) professor - Synonyms
Use the ~ to find synonyms.
Place a tilde (~) before a word, you’ll get results with synonyms for that word.
For example, “holiday ~decorations” would give synonyms like “decor”. - To search within one WEBSITE, use the shortcut term “site:”
For example: Search for the term “professor” at the University of Tennessee website.
When you want to search the content of one particular website,
Type site: and then the website you want to search. Ex: professor site:utk.edu  Expand that to look for keyword phrases in specific websites:
Expand that to look for keyword phrases in specific websites:
For example: “holiday decorations” site: walmart.com
You can type your keywords before or after the search operator.
And you can also use any other search operators with it.- Search for related sites
Use the related: operator.
Type related: and then the name of a site.
This will give you similar sites, such as RiteAid
related: walmart.com - Get info about sites
Sometimes you need to gather a little intel about a site.
Type info: before a URL, to get many different types of information about any site:
Ex: info:wanttoknow.info
This will give you a variety of information about a website. - See older cached versions of a website.
Ex: cache:wanttoknow.info - Search hashtags
This is useful if you’re planning a social campaign, Google can search hashtags from social media networks. Use the pound symbol (#) before the keyword.
Ex: #letsgobrandon
Ex: ##letsgobrandon twitter. - Search for a range of numbers
If you’re shopping by prices, Google can show results within a range.
A minimum value and a maximum value range is indicated by two periods (..) between the numbers.
Example: iPhone $700..$900 - Find Keywords or Phrases in Page Titles:
Use the intitle: operator to find a keyword in the page title.
Ex: intitle:acupuncture - Or find a Phrase in a page title:
Ex: intitle: acupuncture meridians - Find keywords in a webpage text
The intext: operator shows results for a specific keyword in the text of the page.
This is extremely useful if you’re looking for articles.
Ex: intext: acupuncture
Or search for a phrase in page text - Find phrases in a webpage text
Use the operator allintext: will let you find entire phrases in the page text.
Ex: allintext acupuncture meridians - Find phrases in a webpage title
Use the operator allintitle:
Ex: allintitle acupuncture meridians - Find keywords in URLs
Looking for a URL about a certain topic?
You can use the inurl: operator
Ex: inurl:marketing - Find content by certain authors
If you know who wrote an article, use the allinpostauthor: operator.
Ex: allinpostauthor:Jane Barthelemy - Search by filetype
If you’re after a specific filetype, like docx or pdf, use the filetype: operator.
If you’re looking for a specific book in pdf, this search will return results for PDF files:
Ex: History of Money filetype:pdf - Find the Source. This operator allows you to choose a specific source in Google News. (Useful if you have to cite specific news sources when you write a news piece.)
Example: apple source:nytimes.com - Use Parentheses for clarity
Parentheses are used to group words and expressions so that the expression between the parentheses can be used as part of a more complex query. Parentheses isolate expressions in your query from other expressions, especially when creating complex queries using proximity operators and search operators.
For Example: (congressional or executive) and hearing
retrieves documents with both words “congressional” and “hearing,” as well as with both words “executive” and “hearing”. - Search for the word with Max Number of Hits,
Use +The Number of hits “+” operator can specify that documents with more hits on a particular word given preference over documents with hits on other words.Example: +cardin congressional committee
retrieves documents with words “cardin”, “congressional”, and “committee” anywhere inside the document with documents having more hits on “cardin” being given higher relevancy than documents with more hits on “congressional” or “committee”. - Specify Search Language:
Operator lang: to search in a given languageEx: lang:id gives results in Indonesian. Here are a few language codes:- en – English;
- ru – Russian;
- uk – Ukrainian;
- be – Belarusian;
- kk – Kazakh;
- tt – Tatar;
- tr – Turkish;
- de – German;
- fr – French
- id – IndonesianThere are many other language codes: Click here for a list:
https://gist.github.com/JT5D/a2fdfefa80124a06f5a9
And to get your search results in a different language, click here for instructions: https://www.ghacks.net/2018/03/16/how-to-get-google-search-results-for-a-different-language/
Try “Dorking” on Other Search Engines
Warning: Search Operators on Other Search Engines Will Vary. There are no clear rules. Here are a few resources:
- Advanced Search Operators for Yahoo, Bing and Google, from Bruce Clay inc.
- Google hackingentry from Wikipedia
- DuckDuckGo official search syntax
- Bing Advanced Search Tricksfrom Microsoft
- Google Search Help, about refining web searches
- Google, Yahoo and Live Search operators
- Yandex Advanced Search is here: https://search.mediasova.com/en/yandex
- 25 Search Operators in Yandex: https://seosly.com/blog/yandex-search-operators/
5. Try These Interesting Special Searches
Use Internet Archive WayBack Machine to Find Disappeared Articles
The Internet Archive is a very useful source when you know the original URL. Find a copy of an important web page that has been removed or changed:
- Copy the URL (Internet address) of the missing or changed page.
- Go to http://www.archive.org.
- If there is anything in the “Wayback Machine” box, delete it.
- Paste the URL you’ve copied into the box and click the “Take Me Back” button.
- Click on any date listed to see the original article as it was posted on that date.
The above method will show you exactly how the webpage looked on the date it was copied into the archive. However, any website can request not to be listed on the Internet archive, though very few websites have done this. If this is the case, you may still be able to find the article on another website using a quote from the original article.
Here’s how to use the WayBack Machine at the Internet Archive
The Wayback Machine Internet Archive contains old website versions. This is the Internet’s Tardis. Find the Wayback Machine at archive.org. It caches many webpages and allows you to look at them on different dates (unlike the search engine caches that only retain the page the last time it crawled it). Note that it does not capture every change made, but it can be very useful for finding content at some previous time.
Use a Browser add-ons for finding cached pages:
If you use Firefox you can download the ‘Resurrect Pages‘ add-on gives easy access to a number of caches, including Google’s and the Wayback Machine. For Google’s Chrome browser, try the Web Cache extension.
Find WikiLeaks Documents
WikiLeaks is an international non-profit organization that published news leaks and classified media from anonymous sources. Wikileaks was founded by Julian Assange, an Australian Internet activist, and is currently fighting extradition to the United States over his work with WikiLeaks. Wikileaks released online 10 million documents since 2006.
- Find all Wikileaks: https://file.wikileaks.org/file/
- https://file.wikileaks.org/file/… These are Clinton’s emails: https://file.wikileaks.org/file/clinton-emails/
- Securely submit leaks: http://wikileaks.org/#submit
- https://twitter.com/wikileaks
- https://www.facebook.com/wikileaks/
Search Social Networks
Twitter: Use Advanced Search Feature here: https://twitter.com/search-advanced
Instagram: Instagram’s search feature makes it easy to find anything, including users, posts, Reels, hashtags, and locations. Pull up the Instagram search tool and enter the keyword or phrase you’re looking for. You can even search Instagram for filters and effects to use in your Stories and Reels. This wikihow article will teach you 4 easy ways to search Instagram using the mobile app and on the web. https://www.wikihow.com/Search-Instagram
Facebook: Use Facebook’s search feature. Here’s a link that explains it.
https://www.howtogeek.com/282908/how-to-use-facebooks-search-to-find-anyone-or-anything/
Search by Geographic Location, go to Sqoop.com
https://sqoop.com/blog/2016-03-11-geographic-search
Find Geographic Search with Location Filters. A location filter consists of one of the following kinds of criteria:
- Point (WGS84 latitude/longitude) and range in miles
- US state
Google Scholar, Google Books, Journals, Patents, a HUGE Resource
This a huge resource for Books, Articles, Journals, Demographic data: through Google.
Use Google Scholar to find library books near you.
Here’s a tutorial for Scholarly research.
https://journalistsresource.org/home/advanced-research-techniques-google/
The above tutorial is very useful, as it explains how to find PATENTS at min. 25:00 of the above link. Also explains YouTube searches, Google Alerts, Microsoft Academic Search.
How to Use OSINT (Open Source Intelligence)
OSINT is a research method used by militaries, governments, and law enforcement, to collect, evaluate, analyze, and share public information. OSINT is just one branch of intelligence, amongst others which include HUMINT (human intelligence), MASINT (measurement and signatures intelligence), SIGINT (signals intelligence), and IMINT (imagery intelligence). The “open source” part refers to the fact that the information is freely available and comes from public sources.
An OSINT service provider may use sources from Surface Web and Deep Web. For example, they can gather social media content and federal court records that usually require an account to view, as well as web pages that are not yet indexed. AN OSINT service provider usually works collaboratively, with their client to help answer questions and resolve problems.
Searching Tricks and Shortcuts:
- https://filmot.com/ (search YouTube sub-titles which includes deleted videos)
- https://save.tube/download/clip/ (save YouTube clips, partial footage)
- Useful Tools for TruthSeekers (https://pennybutler.com/sleuth-tools/)
- Free Online Video Downloader (https://pennybutler.com/video-dl/)
- More Useful Tools For TruthSeekers: https://pennybutler.com/sleuth-tools/
6. The Deep Web is a Huge Resource of Un-indexed Data.
So far in this article we’ve been discussing the Surface Web, which is indexed and can be searched on search engines.
Together the Deep Web and the Dark Web make up 96% of the internet. They say the Surface internet is just 4%. The raw, un-indexed data “hidden” in the DEEP and DARK WEB is indeed vast. The terms “Deep Web” and “Dark Web” are sometimes used interchangeably, however, they are NOT the same. The “Deep Web” is just the part of the internet which is not indexed on any search engine. The data may not have any specified URL, but it does exist all the same.
As Wikipedia says:
“The biggest weakness of the Deep Web is also its greatest strength: it’s really hard to find anything”.
The Deep Web is web content that’s hidden. It might be previous updates of a mobile app, government databases, financial records, academic records, sealed online wikis etc. It’s just chunks of data that’s not on the surface, not indexed by Search engines, and maybe the owners don’t want you looking at it.
You can publish content on a deep web forum, and most authorities won’t be looking for it. You need protection to be anonymous. MN people use NordVPN and a TOR browser.
7. The Dark Web uses Anonymous TOR Browser and a VPN.
The Dark Web is the more illegal and restricted part of web. Everything is anonymous. To go down into the Dark Web requires a TOR browser and VPN anonymous proxies to access it. I’ve never been there. I understand you’ll find a lot more than “documents”. You may also find hidden government codes, credit cards for sale, human trafficking, drugs, and more. On the Dark Web, secure proprietary software is used on protected communications platforms that can be shared between journalists and sources.
According to the Surface Web, lavish deliveries of ‘lethal aid’ from the US, UK and other NATO countries to Ukraine amid its conflict with Russia have led to a brisk Dark Web marketplace for those same weapons. Ukrainian traders claim to offer not just handguns and body armor, but also ophisticated hardware as Javelin and NLAW anti-tank systems or Phoenix Ghost and Switchblade explosive drones. Click here to see most popular Dark Web Links.
What Can You Buy on the Dark Web?
On the Dark Web you can buy things like mailing lists for social activists, children, sex, meth, cocaine, weed, drugs, injectibles, medicines without prescription, jewelry, credit card services, passports, ID’s, bank details, classes on hacking and other cyber-security skills, tranquilizers, cocaine, heroin, MDMA, LSD, Benzos, and Opioids, paid with Bitcoin or other crypto currencies.
Positive Uses of the Deep and Dark Web
Some people have used the Deep Web to leak sensitive govvt documents, or whistle blowing, in order to anonymously avoid risk and bodily harm.
How to Access the Deep and Dark Web
You need the TOR browser. This is a “browser” with VPN features built in for anonymity. But since Tor is not 100% safe or secure, it is advised to use Tor with a VPN for more security.
To connect to the Dark Web you must access it with the Tor browser, which can be downloaded for free at https://www.torproject.org.
What Are Onion Links on the Dark Web?
Onion links are new type of hidden service domain names on the Dark Web. They can be explored safely via the Tor or Tails browsers. The purpose of using an onionlink system is to make completely anonymous both the information provider and the person accessing the information. More info: https://onionlinks.com
Popular Onion Links include:
- Mixabit– Bitcoin mixer
- OnionLinks– .Onion link directory.
- Bitpharma– Biggest European .onion drug store.
- DarkWebHackers– Dark Web Hackers for Hire.
- Cardshop– USA CVV KNOWN BALANCE & Worldwide CC & CVV .
- DuckDuckGo– A Hidden Service that searches the clearnet.
- The Original Hidden Wiki– The Original since 2013, new v3 Onion Link
- OnionLinks– .Onion link directory.
- The Hidden Wiki– New Hidden Wiki 2023
- Another Hidden Wiki – Another hidden wiki like link collection.
- The Dark Web Pug – Pug’s Ultimate Dark Web Guide .
8. The Internet of Things (IoT) – The Great Reset Connectivity of all digital machines via nodes.
The Internet of Things (IoT) has become a huge topic of discussion in the last few decades. The Internet of Things is when many devices are connected to the internet. The devices could be minicomputers like sensors, actuators, microcontrollers, single-board computers. These
sensors and actuators are given the job of interfacing with the world. Sensors deliver information to the microcontroller which in turn can forward it to a data point via cellular network wirelessly to the Cloud, for analysis, either directly to a web service somewhere on the internet, or through a gateway minicomputer.
Many interconnected machines and objects, each with individual computing capability, extends the power of the Internet exponentially. Already there are many tiny, concealable, collection devices embedded around us and inside us. Maybe your refrigerator could be collecting information about YOU. Amazon has even received complaints that their Alexis devices and electronic vacuums are able to send conversations and compromising photos to central data collection services.
The public selling point of the Internet of Things IoT is to automate everyday life and deliver simplicity, comfort, efficiency by making everyday objects digitally accessible. This gives rise to the idea of SmartCars, Smart Cities, SmartHomes, and SmartSurveillance. Oh Really?
9. Bio-Internet of Nano Things and Smartdust.
What if the Internet is Humans and Bacteria?
 “After the Internet of Things, which transformed the way we live, travel, and work by connecting everyday objects to the Internet, it’s now time for the Internet of Bodies,” says Xiao Liu, fellow at the WEF’s Center for the Fourth Industrial Revolution.
“After the Internet of Things, which transformed the way we live, travel, and work by connecting everyday objects to the Internet, it’s now time for the Internet of Bodies,” says Xiao Liu, fellow at the WEF’s Center for the Fourth Industrial Revolution.
New nanomaterials like graphene have inspired the idea of expanding the Internet of NanoThings (IoNT), which can interact with nano sensors in the human body. Although artificial IoNT frequencies are almost always detrimental to health, there is the huge ethical question of global surveillance and remote control, the great wet dream of the elite of our society. Do you think it will work?
Will we soon be hybrid Human – Machines? The novel paradigm of the Internet of Bio-Nano Things (IoBNT) is a synthesis of human biological functions, synthetic biology (artificial body parts) and nanotechnology, in order to read or control the embedded computing devices in the body. Cellular biochemical functions and electromagnetic energy generated by the body gives us the birth of Internet of Bio-Nano Things (IoBNT), a paradigm-shifting concept for communication and network engineering. We once had stand-lone computers. Then we got machine networks. We connect them to the body for a the biological network.
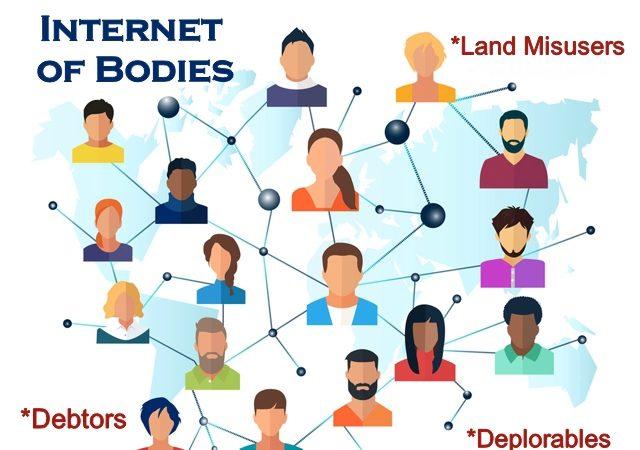 A human energy field is effectively a Wireless Body Area Network (WBAN). This means a wireless network of wearable computing devices may be embedded inside the body as implants. They may be surface-mounted on the body in a fixed position, or may be accompanied devices which humans can carry in different positions.
A human energy field is effectively a Wireless Body Area Network (WBAN). This means a wireless network of wearable computing devices may be embedded inside the body as implants. They may be surface-mounted on the body in a fixed position, or may be accompanied devices which humans can carry in different positions.
Nanoparticles have been widely deployed. They change DNA. They are even in the COVID tests! Nanoparticles and smartdust in your body will plug you into any network via 3G/4G/5G/Wifi/Lifi system using your body as computer interface
Nanodiamonds are used as a carrier in biosensors, probes, bio-implants, and drugs.
These are produced by controlled explosion in a laboratory. Because nanodiamonds are inexpensive to make on a large scale, and have high bio-compatibility, nanodiamonds are widely considered a potential material in bio-electronic applications and quantum engineering. They are also said to be non-toxic, which makes them well suited for insertion in the human body.
Current research focuses on bonding cancer medicine to nanoparticles for better efficiency, as the medicine is released gradually. However, it is possible that ND is toxic for cellular cultures and humans, due to increased oxidative stress.
What are the effects of nanodiamonds on biological life? In one study involving crickets Acheta Domesticus, the Kaplan-Meier survival analysis revealed that ND in concentration of 200 µg per 100 g of food caused a significant decrease in lifespan, due to structural or/and functional changes in the gut.
AI Can Nano-Communicate with Trillions of Bacteria in Your Body!
Microorganisms such as bacteria can communicate effectively with built-in electro-magnetic sensors, information storage and processing within their cells. And that raises an interesting possibility to ask: Why not use bacteria to create a biological version of the internet of things? Some scientists see how this could be possible. E. coli bacteria make a perfect medium for this network. They are motile—they have a built-in engine in the form of waving, thread-like appendages called flagella, which generate thrust. They have receptors in their cell walls that sense aspects of their environment—temperature, light, chemicals, etc. They store information in DNA and process it using ribosomes. And they are tiny, allowing them to exist in environments that human-made technologies have trouble accessing.
Ecoli bacteria are relatively easy to manipulate. The researchers stated: “Bacteria could be programmed and deployed in different surroundings, such as the ocean and ‘smart cities’, to sense toxins and pollutants, to gather data, and undertake bioremediation processes”. This kind of remote biohacking is relatively common and shows the remarkable potential of a bio-internet of things. But there are tremendous risks.
6G wireless technology has been proposed that could use humans as a power source.
Researchers at the University of Massachusetts-Amherst say that 6G could end up using people as antennas. Specifically, 6G telecommunications could take advantage of Visible Light Communication (VLC), like wireless fiberoptics. Fiberoptics use incredibly thin glass or plastic strands to transmit information on flashes of light. These wires are extremely small and fragile. The UMass Amherst team says they have created a low-cost, innovative way of harvesting waste energy from VLC using the human body as an antenna. https://studyfinds.org/6g-use-humans-as-power-source/
10. World-Wide Bio-Internet of DNA Data – This is a Planetary Biosphere Network of Observation and Control.
Maybe the Universal Hive Mind Is Your Body and Soul. The future if the Internet is here.
The worldwide Bio-Internet of DNA Data is a World-Wide Weaponized Biosphere of Observation and Control on a cellular level based on your DNA signature.
Many people do not suspect their body is already commercially available to the cloud since 2005. It’s hard to believe that you can find your body on the web commercially accessible via the same working groups for all wireless devices. It is via the IEEE, the International standards for Electronics and Electrical Engineering. Our biology does certain things automatically. It is wonderful that scientists are finally discovering the IMMENSE intelligence already embedded in our biology. But there’s a huge risk of too much control.
What is Synthetic Biology?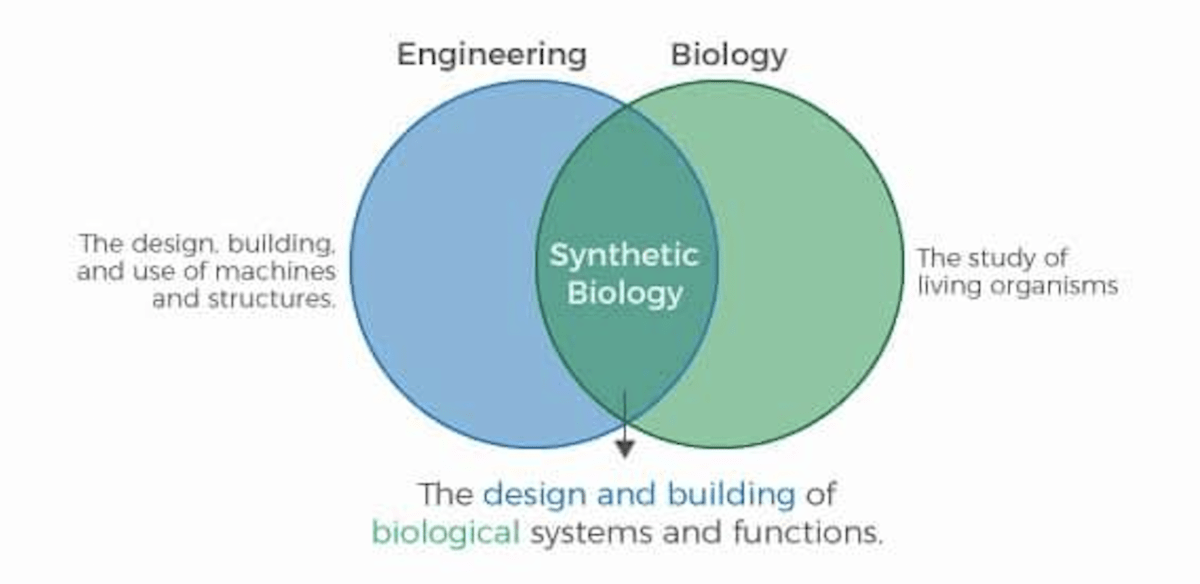
Definition: Synthetic Biology is Engineered, Designed Biological Systems and Functions.
DNA Tracking and Mind Manipulation by AI Happening Now
Your DNA Bio-Resonance is Your Personal Resource. Every person has a unique bio-resonance. These can be coded to message a specific individual, from a supercomputer that knows your bio resonance. Messages can be transmitted from satellite airplane or drone, so that signal would only affect a single person.
The mRNA shot allows for bio-tracking an individual by their living DNA. This connection opens the opportunity for total mind control of a targeted individual. Any organization that possesses a massive DNA database of millions of people can observe and record emotions, thoughts, to an AI program that taps into the resonant frequency of that person. Only the targeted individual would receive the bio electric message. Other people around would not notice anything.
A super-computer can thus monitor and record brain activity of the individual, observing through the eyes of the target, and interpreting the images. The system can download all synapse responses at the speed of light back into a database. The computer can build a cognitive model of your brain. This can be used to create machines, parallel realities and put them into a chip.
The Quantum AI Computer Can Predict your Responses.
An AI computer knows you better than you “know yourself”. It can predict and anticipate thoughts, emotions, and actions of any targeted individual. This information is used to understand how to control YOU, by your personal bio-resonance and history of brain activity. The ultimate goal might be to monitor human beings to record every aspect of human existence, and to make robots as human as possible. Now they’re going after the soul. How to build a soul. They simply copy everything about you into a machine, so that the entire record of your existence has the qualities of a soul. It is a complete simulation of you, and it is immortal. Building false realities with AI to human interface allows for reality manipulation beyond the scope of any human being.
There is no chip required for this interface. It finds existing local networks so that bio coded DNA resonant frequency links targeted individuals to the AI computer database.
The government is now openly warning us.
US lawmakers and military experts are cautioning Americans about risk of DNA testing services, because sophisticated AI computers could use that information to “target” individuals. That means it is already happening.
“There are now weapons developed, that are designed to target specific people,” says Rep. Jason Crow. “…You can actually take someone’s DNA … their medical profile, and you can target a biological weapon that will kill that person or take them off the battlefield or make them inoperable,” he explained at the Aspen Security Forum.
What are the Risks of the IoB – Internet of Bio-Things?
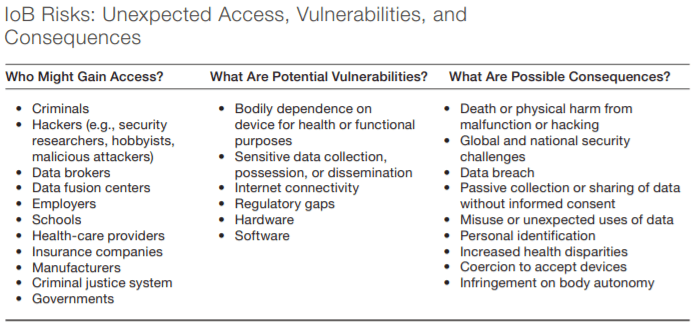
Observation and control of humanity means total power.
The advantages are clear. Called “Adversarial Neural Networks”, they can watch your thoughts with CBANS (Communications Business Automation Networks). Since 2005 this cognitive radar can watch you think in real time. And just like an app on an iPad or cell phone, then they can instigate an event in your body. It could be an event in the brain, the heart, or any organ. Secret government projects have demonstrated how it is possible to observe and potentially control every molecule on the planet. Yes, a wet dream of the controllers.
Gates and Jobs understood the dangers of the cyber world.
They both limited screen time for their children. Why? Because they were aware of the dangers of computer addiction. Steve Jobs did not let his children play with the iPad that he helped create. Interviews with Bill Gates, Steve Jobs, and other tech elite reveal they saw its dangers to society. Many wealthy Silicon Valley parents grasp the habituating power of smartphones, tablets, and computers, so they make strict family rules for computer use.
11. The Universal Digital Hive Mind of Transhumanism Is Your New Body and Soul.
AI-directed Hive Mind Network Can Lead the Global Hive Mind.
When a computer links Your Bio-Resonance to the AI Network, an AI Quantum computer “learns” as it goes. For example, the D-Wave Abiatic Quantum Computer fuses our thoughts into the e-commerce system. The D-Wave Quantum computer can contain the frequencies of 7 billion human brains, the entire Earth population. Since this computer is self-learning to be human, it monitors every human to predict and direct emotional behavior. It seems now that every one of us is monitored and our brain simulation stored to measure our thought patterns and to determine our future actions.
DNA Frequency Bioweapon Links Targeted Individuals to AI Hive Mind Control Grid
 How many Targeted Individuals Have Already Been Shadow-Destroyed?
How many Targeted Individuals Have Already Been Shadow-Destroyed?
“The way this technology works is that a complete DNA profile is obtained from the targeted individual and then this DNA information is used to determine the resonant frequency of the DNA itself. The resonant frequency is then used to fine-tune the technology the radio frequency signals, the microwave auditory effect and all the other aspects of the technology to tune it perfectly to the resident frequency of the targeted individual’s DNA. Then they can read your thoughts verbatim as they occur within your own mind. We can generate an electronic signal that’s characteristic for the DNA. This can read DNA from solution, and your blood is a solution. It’s a liquid. We can decode it into a form that can be read by a computer. And in a way you can think about DNA as a digital information moving through a tube. Now if we can tap into that tube like a network and we can read that information we can intercept what’s happening in people.
“Once they’ve found the DNA resonance of an individual, they can transmit to the individual from satellites or cell towers or aircraft or any number of ways and that signal will only affect you and nobody else in other words everybody standing next to you would ever guess. You can make any person an extension of the internet.”
https://www.bitchute.com/video/GYJyJDJISX2B/
This Pfizer patent application – approved on August 31st, 2021- is for the purpose of remote contact tracing of all vaccinated humans worldwide. They are now connected to the “internet of things” by a quantum link of pulsating microwave frequencies of 2.4 gHz or higher from cell towers and satellites directly to the graphene oxide held in the fatty tissues of all persons who’ve had the death shot. Read that AGAIN!Your organs are already now connected to the Metaverse.

All humans now carry permanent lifetime body sensors connected via satellites, drones, nodes, and ley lines. Although publicly you would be ridiculed for thinking this, they are mapping your soul to observe past lives by reading it. Since 2005 the multi-quadrillion-node earth network has been running data through the human body utilizing its natural electrical conductivity in whole or in chakra network segmented photonic parts.
Brain chip interface to the hive was implemented in 2013. But you don’t need a chip in your brain at all. You are now completely wireless connected via satellites. Even your precognition is being watched.
NEURALINK!
To further enhance your computer connection and capabilities, you can install the new Neuralink brain chip by Elon Musk. A brain interface chip supposedly allows you to control computers and machines with your mind.
The World Wide BioSphere of all bodies and souls has already been designed, and the targets have been contacted.
Led by Secret military research, recently the Globalists, Big Pharma, High Tech and world government minions have seized our lives in the most evil ways. They do not intend to let go until their nightmare agenda to merge human beings with Artificial Intelligence-Human 2.0-has revolutionized our lives, enslaved us, and taken control of our world. This is NOT a “theory” anymore – it’s a global conspiracy.
How did they plan to achieve this malevolent goal? With The IoBNT of course. First, they must use vaccines to hack into our DNA, the God Code to remove the light within us: the Divine Blueprint. Then, they plan to splice into our DNA code, a messenger or numerical mark that makes people more docile with no soul interest in evolutionary ascension. Unbelievable as it seems, their ultimate goal is to steal our universal unlimited resource, our souls. And to remove any of us who object.
We are already linked via satellite networks operated by many vendors including SpaceX, which provide satellite Internet and mobile phone service coverage worldwide.
Prince Warned us in 1999
“There Is a War Going On, The Battlefield Is in The Mind, And the Prize Is Your Soul!”
Don’t Be Fooled By The Internet
 The Human Biofield is a DNA-Generated Body Part, Now on Sale via the Web.
The Human Biofield is a DNA-Generated Body Part, Now on Sale via the Web.
A whistle-blower recently revealed an agenda of secret military projects that our bodies have already been made commercially available to the cloud since 2005. IEEE is the International standards for Electronics and Electrical Engineering. You will find your body on the web and commercially accessible via the same wireless working groups for all wireless devices. How did this happen? Why are you tired? Maybe it’s the invisible energy fields around you are sucking your life force. How can we gain access to the biosensors that are magnetically routing our data for sale?
Hacking the Soul and Reading Your Digital Aura.
The human bio field, formerly known as the aura is 80% of your immune system and 40-60% of our endocrine system. The global internet of behaviors guarantees that your actions, thoughts, emotions and marketing choices are now being calibrated.
Why didn’t anybody tell you that you were already wireless? Because they don’t want to give you the remote control to your own body.
A Warning from Master Li Hongzhi, founder of spiritual practice Falun Gong:
“The aliens have introduced modern machinery like computers and airplanes. They started by teaching mankind about modern science, so people believe more and more science, and spiritually, they are controlled. Everyone thinks that scientists invent on their own when in fact their inspiration is manipulated by the aliens. In terms of culture and spirit, they already control man. Mankind cannot live without science.
The ultimate purpose is to replace humans.
If cloning human beings succeeds, the aliens can officially replace humans. Why does a corpse lie dead, even though it is the same as a living body? The difference is the soul, which is the life of the body. If people reproduce a human person, the gods in heaven will not give its body a human soul. The aliens will take that opportunity to replace the human soul and by doing so they will enter earth and become earthlings.
When such (soulless) people grow up, they will help replace humans with aliens. They will produce more and more clones. There will no longer be humans reproduced by humans. They will act like humans, but they will introduce legislation to stop human reproduction.”
Are you OK with this plan?
If you wish to be part of this dystopian future, then all you have to do is watch your TV, get all your shots, and stay connected to your devices, with no regard for your own body or physical health.
12. What was Apple Founder Steve Jobs’ Warning for the World in the film “John Carter”?
 As a major owner of Pixar and Disney, Steve Jobs inspired the movie “John Carter”.
As a major owner of Pixar and Disney, Steve Jobs inspired the movie “John Carter”.
I believe the movie should be regarded as a warning and wake-up call. The movie “John Carter” is a 2012 American science fiction action-adventure film of interplanetary adventure. The film was dedicated to the memory of Steve Jobs. In the movie: Captain John Carter (Taylor Kitsch) is inexplicably transported to Mars where he becomes reluctantly embroiled in a conflict of epic proportions amongst the inhabitants including tribal chief Tars Tarkas (Willem Dafoe) and the captivating Princess Dejah Thoris (Lynn Collins).
The hidden message is to honor life, serve the soul, move beyond the limited world, to be a force of light and love, to refine yourself to achieve your destiny of eternal life.
John Carter finds himself in a bizarre world on the brink of collapse, in a universe ruled by time-traveling, Godless elites who live forever. They care for nothing but power and the “game” of manipulating the masses for sport, by shapeshifting and betraying any cause for a lark. The elite use their wealth in the violent design of societies, baiting the rise and fall of rival alien empires at their whim.
Carter rediscovers his humanity when he realizes that the survival of Earth and its people rests in his hands. He travels through time, fakes his own death, and returns to Mars to claim his destiny of freedom.
Watch the movie playlist here on YouTube.
13. Connecting the Dots: Use Your Biofield as Your Sacred Resource for Universal Source Consciousness of INTENT. The human biofield Just Became a DNA-Generated body part.
Strengthen your Spiritual Biofield. “Know Yourself” better than the Digital Field. Your Sacred Resource of Universal God Consciousness is your “INTENT”
 Physical life means we are part of a universal energy field. The energy field of Nature fosters life. But artificial or anti-biological frequencies do not foster life.
Physical life means we are part of a universal energy field. The energy field of Nature fosters life. But artificial or anti-biological frequencies do not foster life.
Defensive protection means we must have full control over all of our body parts, including the precious biofield that is DNA-generated. Make sure your biofield is under control, as the electromagnetic battle is here and now. Learn how to defend yourself at the cellular level with your natural, God-given body part, your energy field, that we were never taught about. Protective devices can be helpful, but here we mean your God-given aura.
The human energy field is already built into our biology. The chakras and meridians are our electromagnetic sensor nodes. We already own the shared telepathic tools. We don’t really need remote sensors or embedded devices for the body to navigate the changing electrical forces of God’s universe?
Want to Reclaim Your Body and Soul?
To stay strong means we stop giving our power away. Instead we entrust our future life over to the most powerful and positive force in the universe. The God field. Call it what you like. This almighty force is already in your DNA. The bio-field aura is your body part. It can sense the invisible biotechnology that invades Earth. And it can be resilient.
In the process we must clean up the body functions that got gummed-up with toxic accumulation. We clean up our mind from toxic thoughts. We clear the memory of trauma that weighs heavily on us.
This entire digital TRANSHUMANIST issue is a warning, wake-up call, and a culling of humanity. We must move beyond physical solutions. The best solutions are meditation, raising the bio-frequency to live with spiritual awareness and INTENT.
There are many tools for this, and it is a life process. Physical cleansing, Meditation, Self-Healing, Raising your Vibration, Qigong, Yoga, Mindfulness. What’s best for you?
Thanks for showing up!
Srijana
Suggested Research:
- https://www.wanttoknow.info/g/internet_search_techniques
- https://www.hackread.com/dark-web-search-engines-tor-browser-2022/
- https://www.guru99.com/private-search-engines-anonymous-no-tracking.html
- https://webwriterspotlight.com/tips-to-nail-online-research
- https://file.wikileaks.org/file/clinton-emails/
- https://www.ivacy.com/blog/dark-web-search-engine/
- https://www.thedarkweblinks.com/dark-web-browsers/
- https://www.comparitech.com/blog/vpn-privacy/access-dark-web-safely-vpn/
- https://www.vpnmentor.com/blog/whats-the-dark-web-how-to-access-it-in-3-easy-steps/
- https://drfone.wondershare.com/dark-web/dark-web-browser.html
- https://vpnalert.com/resources/how-to-get-on-dark-web/
- https://www.wizcase.com/blog/safely-find-the-best-dark-web-sites/
- https://thehiddenwiki.org
- https://thehiddenwiki.org/blog/
- https://www.csoonline.com/article/3249765/what-is-the-dark-web-how-to-access-it-and-what-youll-find.html
- https://www.computerhope.com/issues/ch000082.htm
- https://www.govinfo.gov/help/search-operators
- https://search.mediasova.com/en/duckduckgo
- https://www.deepwebsiteslinks.com/facts-about-the-deep-web/
- https://thehiddenwiki.org/wp-content/uploads/2021/12/hiddensites.jpg
- https://neilpatel.com/blog/google-search-operators/
- https://www.skopenow.com/news/surface-deep-and-dark-web-osint-applications
- https://www.olivebiodiesel.com/censortest/
- https://journalistsresource.org/home/advanced-research-techniques-google/
- https://www.boxpiper.com/posts/google-dork-list
- Search Smart by Dorking, https://kit.exposingtheinvisible.org/en/google-dorking.html
- https://computers.tutsplus.com/tutorials/how-to-find-anything-online-with-advanced-search-techniques–cms-21154
- https://seosly.com/blog/yandex-search-operators/
- https://www.nightingale-collaboration.org/making-a-complaint/tools-a-resources/finding-old-web-pages/39-finding-deleted-and-changed-webpages.html
- The WayBack Machine Internet Archive, https://archive.org/web/web.php
- Geographic Search: https://sqoop.com/blog/2016-03-11-geographic-search
- What is OSINT & How to Conduct Investigations with Open Source Data, https://www.skopenow.com/news/what-is-osint-how-to-conduct-investigations-with-open-source-data
- https://news.cybersixgill.com/5-scary-trends-we-found-on-the-dark-web/
- https://medium.com/swlh/internet-of-things-whats-that-d3fb018aa7b8
- https://www.technologyreview.com/2019/11/01/132100/the-scientists-who-are-creating-a-bio-internet-of-things/
- Internet of Nano-Things and Wireless Body Area Networks (WBAN)
- ByFadi Al-Turjman, https://www.taylorfrancis.com/books/edit/10.1201/9780429243707/internet-nano-things-wireless-body-area-networks-wban-fadi-al-turjman
- https://publications.hse.ru/articles/146368739?ysclid=lcft6yq92750968960
- https://odysee.com/@Psinergy:8/trim.D5E8F851-4FF8-483C-B72A-7590D29617E2:4
- SABRINA-CHANNEL: The human biofield is a dna generated body part, https://odysee.com/@Psinergy:8
- https://arxiv.org/pdf/1809.08914.pdf
- https://studyfinds.org/6g-use-humans-as-power-source/
- DNA Frequency Bioweapon Links Targeted Individuals to Artificial Intelligence Hive Mind Control Grid,
https://www.bitchute.com/video/GYJyJDJISX2B/ - DNA Frequency Bioweapon Links Targeted Individuals to Artificial Intelligence Hive Mind Control Grid, https://www.youtube.com/watch?v=iEgZQgP9SMs
- Good Testimonial of T.I. Targeted individual Gangstalking / Organized Stalking TargetedIndividuals,
- https://odysee.com/@acurrentconspiracyacc:2/good-testimonial-of-t-i-targeted:a
- https://www.researchgate.net/publication/303541423_The_effects_of_nanodiamonds_on_lifespan_growth_food_consumption_and_body_mass_in_the_house_cricket_Acheta_domesticus
- https://nypost.com/2022/07/24/rep-crow-warns-enemies-could-use-dna-tests-to-kill-americans/
- DNA Frequency Bioweapon Links Targeted Individuals to Artificial Intelligence Hive Mind Control Grid, https://www.youtube.com/watch?v=iEgZQgP9SMs
- https://www.brighteon.com/53c0ac9f-a23d-4f79-b817-f5e8def95174
- https://stateofthenation.co/?p=61571
- https://write.as/uvgz4q02oigu390v
- https://fiveseasonsmedicine.com/master-li-hongzhi-on-aliens/
- https://pennybutler.com/sleuth-tools/
- https://searchvpn.org/is-tor-browser-safe-to-use/